- 本公司資訊安全之權責單位為資訊課,負責規劃、執行及推動資訊安全管理事項,並推展資訊安全意識。
- 本公司稽核室為資訊安全之查核單位,若查核發現缺失,旋即要求受查單位提出相關改善計畫,並定期追蹤改善成效,以降低內部資安風險。
- 相關資訊風險評鑑結果應該提報權責主管簽核認可。
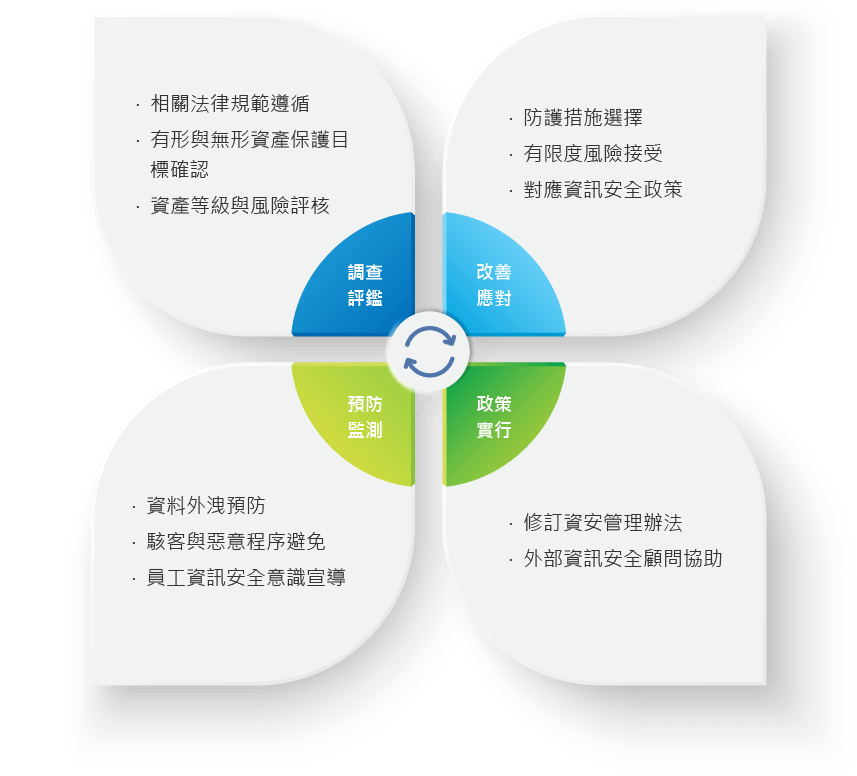
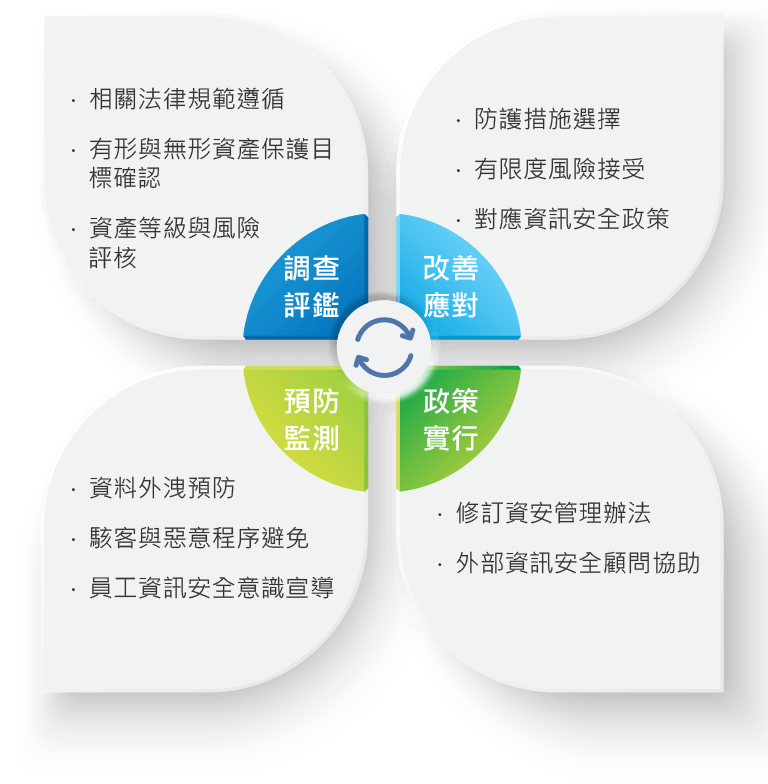
資訊風險管理循環
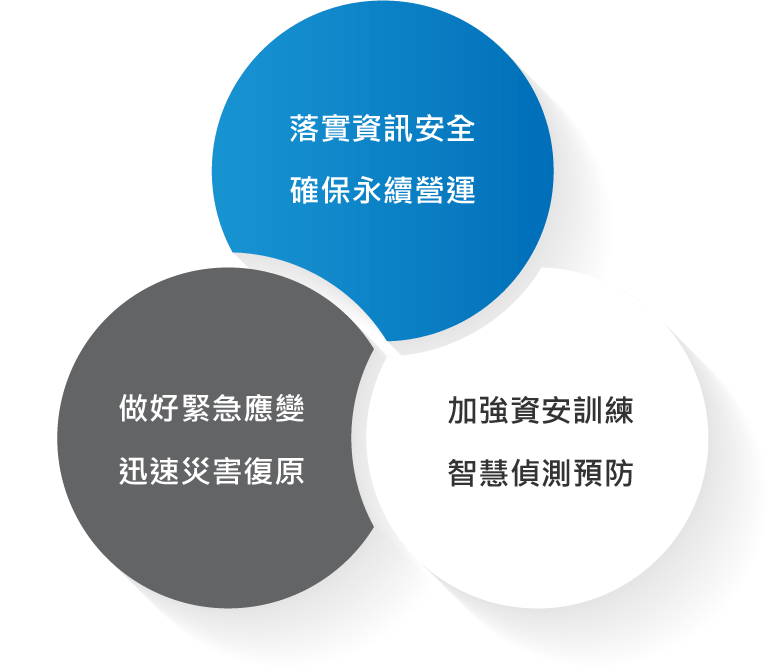
資訊安全政策
本公司企業堅持正大光明,永續經營的企業使命與理念,特頒布此資訊安全管理政策。確保公司內部資訊系統有效維持運作、保持機密性、完整性與可用性。
本政策旨在讓同仁於日常工作時有一明確指導原則,所有同仁皆有義務積極參與配合推動資訊安全管理政策,以確保本公司所有職員、資料、資訊系統、設備及網路之安全維運,並期許全體同仁均能了解、實施與維持,以達資訊持續營運的目標。
現行執行
- ‧ 強化電腦權限管理
- ‧ 定期資安稽核作業機制
- ‧ 帳號權限盤點
- ‧ 落實還原演練實戰
- ‧ 異地資料備援/備份
- ‧ DRM文件保護軟體
- ‧ 高可用性主系統架構
中長期目標
- ‧ 端點防護引入
- ‧ 資料傳輸流量監測
- ‧ 行為軌跡紀錄
- ‧ 跨境異地資料備援 / 備份
- ‧ 定期強化員工資安意識
- ‧ 社交軟體限制與監測
- ‧ 智慧入侵偵測預防
公司資訊安全管理措施推動成果
近年來資訊服務最大的風險來自於加密貨幣的興起助長的大量勒索病毒風潮。
對於此類型攻擊,公司的對應政策分終端用戶設備與後端伺服器,前端一般使用者設備安裝防毒防駭軟體進行保護,並要求人員重要營運資訊應存在於系統、管制儲存區用以降低單點存放風險,人員操作意識的預防則投資網頁過濾、郵件過濾等服務、設備,並加強人員資安意識、規劃社交工程演練、資安事件宣導。後端則是透過321備份法則,維持管制儲存區、虛擬機的快速回復能力。

本公司注重資訊安全與個人資料保護,制定個人資料保護管理辦法,適用範圍涵蓋公司內、公司外與各利害關係人資料之傳遞與使用約束,於收集個人資料時取得同意、並定期盤點個資使用情形,包含實體文件與系統個人資料,採取權限管控,以掌握個資洩漏風險防範與因應對策。
近三年個人資料盤點情形
| 年度 | 個人資料盤點時間 | 個人資料外洩事件 | 個資申訴案件 |
|---|---|---|---|
| 2024 | 05/24 | 0 | 0 |
| 2023 | 04/21 | 0 | 0 |
| 2022 | 04/29 | 0 | 0 |
違反個資法申訴管道:
獨立檢舉信箱:
檢舉專線:04-7582827 分機2201、2001
請點選連結至 個人資料保護政策

